eMSP Software Development: Architecture Patterns, APIs, and the Decisions That Decide How Far You Scale

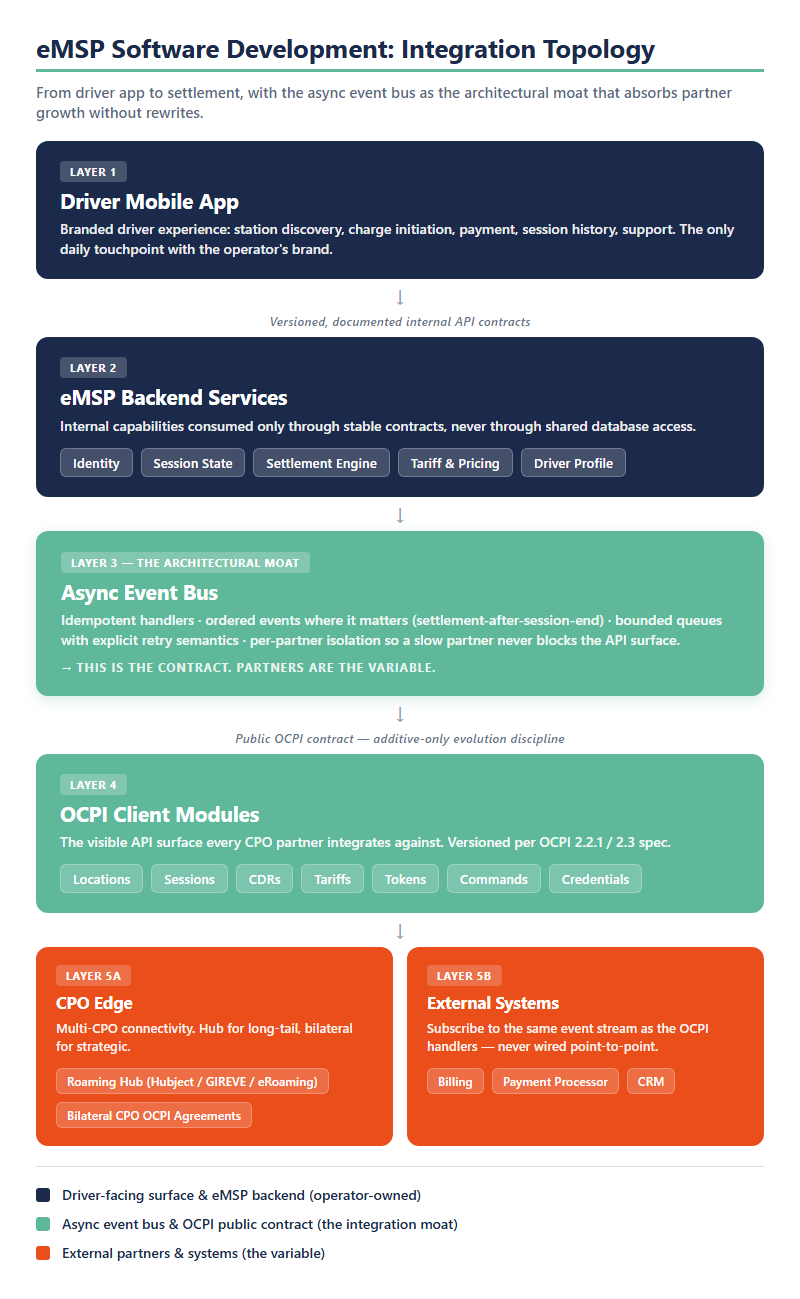
eMSP software development is the engineering work behind every credible e-mobility service provider platform: the API contracts, the integration topology, the observability layer, and the phasing decisions that decide whether a platform running the first hundred drivers can also run the next fifty thousand. The architecture decisions deferred at month one are the ones operators pay for at month eighteen, when an Open Charge Point Interface (OCPI) Sessions queue that worked for a single Charge Point Operator (CPO) partner cannot handle bilateral agreements with twelve, or when settlement clocks drift by minutes because no one designed the event ordering. The eMSP platforms that scale gracefully are not the ones that picked the best stack; they are the ones that chose an api-first emsp architecture with stable contracts, async-by-default integration patterns, and observability built in rather than bolted on. This guide walks the technical buyer through the engineering decisions that distinguish an eMSP software development project that delivers a production-ready platform from one that delivers a launch followed by a rewrite.
Why eMSP Software Development Is an Architecture Problem, Not a Stack Problem
The conversations that produce a failed eMSP platform usually start with the wrong first question. Teams ask whether to build on Node or Go, whether to deploy on Kubernetes or serverless, whether to use Postgres or a document store. Those are real choices, and they matter at the margin. They are not what decides which platforms survive the third partner integration and the second market expansion.
The first question is structural. Where do the event boundaries sit? Which of them must outlive any single CPO relationship, any single payment processor, any single roaming agreement? The platforms that hold up at scale are the ones whose internal contracts were designed to absorb integrations that did not exist when the platform shipped. The platforms that hit a ceiling are the ones whose contracts assumed the first integration would also be the last.
That ceiling is not theoretical. It is the operator with a working pilot at one thousand drivers, a clean stack chosen by a competent team, and a production migration scheduled for the next quarter that quietly turns into a six-month rewrite. Under load, the OCPI Tokens module reveals that the synchronous authorization path was the only path. The stack held; the architecture buckled. For the deeper architecture context that sits behind these specific engineering decisions, see the four-lever eMSP platform thesis; this article walks the layer below it, the contracts and queues and traces.
The architecture problem above also presupposes a role decision. The contracts, queues, and traces this article walks through are designed for a platform serving an eMSP, a CPO, or — increasingly in 2026 — both roles on one integrated stack. The role-and-revenue decision precedes the engineering decisions: which margin the platform captures (driver-side, asset-side, or both at the OCPI settlement layer), which forcing functions bind first, and whether the second role becomes mandatory inside the 24-month strategy horizon. Our eMSP vs CPO role-and-revenue decision companion walks through that decision before the engineering work begins.
API Design: Stable Contracts Beat Clever Abstractions
eMSP platforms have two API surfaces, and most teams design only one of them deliberately. The visible surface is OCPI — the modules every CPO partner integrates against: Locations, Sessions, CDRs (Charge Detail Records), Tariffs, and Tokens. The invisible surface is the eMSP’s internal contract between identity, session state, settlement, and the driver app. Both surfaces will evolve. Only one of them can change without breaking somebody else’s production system.
The teams that ship api-first emsp platforms, where every internal capability is consumed through a versioned, documented contract rather than shared database access or service-internal call chains, get one specific advantage that compounds: their fourth, fifth, and sixth integrations cost roughly the same engineering hours as their first. The teams that built clever internal abstractions instead, with service classes that “encapsulate” identity, sessions, or settlement, pay the integration tax in full each time. Every new partner reveals which abstractions leaked into which assumption.
Contract evolution discipline is the moat. Additive changes (new optional fields, new endpoints, new event types) never break consumers. Deprecation windows give partners months to migrate. Breaking changes are versioned, scheduled, and announced, never deployed under the guise of “minor improvements.” The discipline reads like overhead in week one. By year three, it is the difference between an OCPI 2.2.1 to 2.3 migration that ships in two sprints and one that consumes a planning quarter.
| Change Type | Breaking? | OCPI Module Impact (Example) | Recommended Evolution Path |
|---|---|---|---|
| Add a new optional field | No | New last_updated field on Sessions |
Deploy whenever; well-designed consumers ignore unknown fields gracefully. No deprecation window needed. |
| Add a new endpoint | No | New /cdrs/search endpoint on the CDRs module |
Document, version-bump the module spec, announce to partners. Existing endpoints remain unchanged. |
| Add a new event type | No | New SessionPaused event on the internal async bus |
Publish in parallel with existing events; consumers opt in by subscribing. Idempotency keys cover replay. |
| Make an optional field required | Yes | auth_id becomes required in Tokens authorize requests |
Quarter-long deprecation window, module version bump, partner-by-partner migration tracking with deprecation logs on every legacy call. |
| Change a field’s type or semantics | Yes | cost changes from EUR-cents integer to a typed Money object |
New endpoint at the next major module version (e.g., 2.3 alongside 2.2.1); both versions co-exist for 6+ months while partners migrate. |
| Remove a field or endpoint | Yes (high-impact) | Sunset of a legacy /credentials endpoint |
Announce 2+ quarters in advance; per-partner migration tracking; deprecation logs on every call before removal; a hard cutover date that has been communicated repeatedly. |
The OCPI module surface is the canonical reference for what disciplined API evolution looks like in production. The OCPI 2.2.1 protocol architecture is itself an exercise in additive-only evolution: every module version is backward-compatible at the message level, deprecations are announced quarters in advance, and partners run mixed versions during transition windows without either side breaking. eMSP platforms whose internal contracts adopt the same discipline inherit the same property.
Integration Topology: Async-First Is Not Optional
The single largest predictor of whether an eMSP platform scales gracefully past twenty thousand drivers is the topology of its integration layer. Synchronous OCPI flows that worked fine in pilot break in three predictable ways at scale. CDR backpressure from a slow CPO partner stalls settlement clocks for every other partner sharing the same processing pipeline. Tokens authorization queues collide with Sessions update streams when both spike at peak charging hours. A single CPO whose API latency degrades from 200 ms to 2 seconds becomes the latency floor for the entire eMSP API surface, because there is no isolation boundary between partners.
Async-by-default integration patterns are the architectural answer. The eMSP backend publishes events (session started, session ended, CDR received, settlement computed) onto an internal message bus. Handlers consume those events with explicit retry semantics, bounded queues, and idempotency keys that prevent duplicate processing when a partner retries an upstream call. Event ordering is enforced where it matters (settlement must follow session-end) and relaxed where it doesn’t (Locations updates can apply in any sequence). The result is a platform that absorbs ten-times growth without rewriting the integration layer, because the bus was always the contract; the partners on the other side of the bus were always the variable.
The teams that built async-first from day one rarely talk about it; the pattern is invisible when it works. The teams that retrofitted async into a synchronous platform after a scaling incident remember the experience for years. The cost difference between the two paths is the cost of redesigning a production data model under load. Ecosystem partners on the orchestration side, including AutoGrid, Uplight, and Enode, are themselves async-first systems; eMSPs that integrate with them through synchronous wrappers create a topology mismatch that surfaces as inexplicable latency in the second year. The integration shape the ecosystem already runs is the integration shape the eMSP should adopt.
Implementation Phasing: Three Architectural Decisions That Don’t Defer
Three decisions in eMSP software development do not survive being deferred to phase two. Once a platform ships with the wrong answer on any of them, the cost of revisiting compounds quarterly until a rewrite is cheaper than continued maintenance.
The first is settlement-engine ownership. The CDR-to-billing pipeline is the platform’s revenue muscle. eMSPs that outsource it to a payment processor’s hosted settlement service save engineering hours in week one and pay vendor margin on every transaction for the next five years. eMSPs that own settlement from day one carry more code, more tests, and more on-call surface, and capture the entire margin per session indefinitely. The economic crossover for an eMSP growing past five thousand drivers arrives faster than most teams expect, because settlement margin scales with transaction volume while engineering cost scales with feature complexity.
The second is driver-identity model. A federated model issues per-CPO OCPI Tokens, one per partner relationship, and keeps the driver’s canonical identity inside the eMSP. A siloed model uses a single eMSP identity across every CPO and pushes the federation problem onto the partner. The choice determines every downstream OCPI Token flow, every roaming-agreement re-papering, every user-experience possibility for the next five years. Federated identity costs more to build and is the only path that supports multi-market expansion without a rebuild. Siloed identity ships faster and locks the platform to a single-market posture before the marketing team finishes the launch deck.
The third is observability. Bolt-on observability fails predictably, because the events the operations team needs to see during the first production incident are events the platform was never instrumented to emit. eMSP platforms with observability designed in (structured logging, distributed traces across the async bus, metrics that name the business operations: sessions per minute by partner, CDR settlement latency by region, Token authorization success rate by Identity Provider) debug their first scaling incident in hours. Platforms with observability added after the first incident debug their second incident in days, because the instrumentation gap that surfaced in incident one is also the gap during incident two.
These three decisions sit inside the EU Alternative Fuels Infrastructure Regulation (AFIR) compliance landscape too: multi-market eMSPs operating across European markets need federated identity and audit-grade observability to satisfy AFIR’s price-transparency and ad-hoc-payment requirements. The regulatory clock is no longer hypothetical — what gets architected now will be on the ground for a decade.
| Decision | Phase 1 (Must Decide Before First Production Code) | Phase 2 (Effectively Locked In by ~Year 2) | Phase 3 (Rewrite Cost If Revisited) |
|---|---|---|---|
| Settlement-Engine Ownership | Own the CDR-to-billing pipeline in-house, or outsource to a payment-processor’s hosted settlement service. The choice drives the platform’s revenue-margin baseline for its operating lifetime. | Once outsourced, the team has no in-house knowledge of CDR validation, dispute handling, or settlement reconciliation. Vendor lock-in deepens with every active billing relationship. | 4–9 months of engineering work to re-internalize settlement, plus migration of every active billing relationship and a parallel-run period to validate parity before cutover. |
| Driver-Identity Model | Federated (per-CPO OCPI Tokens with canonical identity held at the eMSP) versus siloed (a single eMSP identity used uniformly across all CPOs). The choice determines every downstream OCPI Token flow and roaming agreement. | Every CPO partner integration is built against the chosen model. Migration to the alternative requires re-papering every active roaming agreement. | 6–12 months of architectural rebuild plus partner-by-partner re-papering; some legacy partners may never complete the migration and stay on the old model permanently. |
| Observability Stack | Designed in: structured logging across all services, distributed traces across the async bus, business-named metrics (sessions per minute by partner, settlement latency by region, Token authorization success rate by Identity Provider) from day one. | The first scaling incident reveals the instrumentation gaps; the second incident reveals the same gaps. Observability gets patched incident-by-incident rather than designed comprehensively. | 3–6 months of cross-cutting engineering work to retrofit observability without breaking running code. The opportunity cost in feature velocity during the retrofit dwarfs the direct engineering cost. |
When eMSP Integration Becomes the Whole Job
Once an eMSP platform serves more than three CPO partners, plus a billing system, plus a Customer Relationship Management (CRM) tool, plus a payment processor, integration is the engineering work. Building eMSP-side features stops being the constraint on shipping; the constraint becomes whether the integration layer absorbs the next partner without a fan-out of bespoke adapters.
The first decision in that phase is whether to route OCPI traffic through a roaming hub or through bilateral agreements with each CPO. Roaming hubs (eRoaming, Hubject, GIREVE) collapse N partner integrations into one hub integration, with the trade-off that hub policy and pricing pass through to the eMSP’s economics. Bilateral OCPI agreements keep eMSP control over each relationship at the cost of carrying N integrations directly. The right answer is rarely “one or the other”; it is usually “hub for long-tail partners, bilateral for strategic accounts,” with a topology that supports both without rewriting the underlying EV roaming patterns.
The second decision is the topology that connects billing, CRM, and payment. eMSPs that wire those three systems point-to-point with the eMSP backend end up with five integrations and twenty-five potential failure modes by year two. eMSPs that publish the same internal event stream the OCPI handlers consume — session ended, CDR validated, settlement computed — and let billing, CRM, and payment processors subscribe to that stream, end up with one integration shape and predictable failure modes. Security and audit posture matter equally here: an ISO/IEC 27001:2022 information-security baseline is now table stakes for any eMSP serving enterprise fleet or utility customers, and the controls are far cheaper to design in than to retrofit.
The CPO-side companion question — how Charge Point Management System (CPMS) software relates to eMSP software in the same operator’s environment — sits in the CPMS development domain, with its own integration architecture. eMSP teams whose operators run both surfaces benefit from making the eMSP/CPMS boundary explicit in the topology rather than implicit in shared code.
The Architecture Decisions That Compound for Five Years
eMSP platforms do not fail in deployment. They fail in the third year, when the decisions deferred in design sprint one have compounded into a rewrite no one budgeted for. The contract that was easy to break in week six is now consumed by twelve CPO partners. The synchronous queue that worked at one thousand drivers is now the bottleneck at thirty thousand. The bolted-on observability that surfaced the first incident is still the gap during the fourth. The settlement-engine outsourcing that saved a sprint in phase one is now thirty percent of the platform’s gross margin paid out to a hosted vendor on every transaction.
The eMSP software development teams that ship platforms operators can still operate in 2031 are the ones that made three decisions deliberately in design sprint one: api-first emsp contracts with explicit evolution paths, async-first integration topology with observability built in, and ownership of the settlement and identity surfaces from day one. Every subsequent architecture choice becomes a defense of those three commitments. The first hundred drivers are easy. The architecture is for everything that comes after.
The companion to these engineering decisions is the buyer-side capability audit. The engineering work above asks how to build a platform that scales; the audit framework asks what capabilities the platform must have against 2026 forcing functions — AFIR, ISO 15118-20 plug-and-charge, OCPI 2.2.1 hub maturity, V2G market entry, and FERC Order 2222 / EU CER aggregation. Our eMSP platform features 2026 capability checklist organizes that audit across five capability categories (driver, operator, settlement, compliance, integration) with a Pass/Watch/Fail rubric an operator can run against the platform they own, the one they are about to procure, or the one they are about to build.
For teams evaluating the engagement shape that fits a particular phase, the custom eMSP platform engagement page describes the commercial path; the eMSP Engine accelerator path describes the middle option for operators who want production-grade architecture without a clean-sheet build; and the driver app development companion covers the driver-facing surface that sits on top of the eMSP backend.
Frequently Asked Questions
eMSP software development is the engineering work of designing, building, and operating the platform that lets an e-mobility service provider authenticate drivers, route charging sessions across CPO networks, validate Charge Detail Records, settle revenue, and operate a driver-facing application. It spans backend API design (typically OCPI-compliant), integration with billing and payment systems, observability and security tooling, and the driver mobile experience. For the platform-investment thesis behind these engineering decisions, the four-lever eMSP platform thesis walks through where the structural priorities sit.
Platform development is the ecosystem-investment view: which strategic architectural choices receive the engineering and product budget over a multi-year horizon. Software development is the execution view: the API contracts, integration topology, async patterns, observability layer, and phasing decisions that turn the platform vision into a production system. The two are complementary. The four-lever eMSP platform thesis sets the strategic frame; this article describes the engineering decisions that deliver it.
Yes for any platform that will serve more than one partner integration. An api-first emsp design exposes every internal capability through a versioned, documented contract rather than through shared database access or service-internal call chains. The discipline reads like overhead during the first integration. By the fourth or fifth partner, it is the difference between adding partners in sprints and adding partners in quarters. eMSP teams that defer api-first design until “we need it” usually need it about six months before they realize, and pay the migration cost on top of the platform cost.
The honest range depends on whether the team builds clean-sheet or uses an accelerator. Accelerator-led builds, which inherit proven OCPI modules, identity scaffolding, and reference integration patterns, typically reach a production-ready phase-one platform in 12 to 20 weeks. Clean-sheet custom builds take 8 to 14 months for the equivalent scope, because every decision described above is made from scratch rather than inherited. The eMSP Engine accelerator path is the middle option for teams that want production-grade architecture without a year-long greenfield project. The custom eMSP platform engagement page describes the full bespoke path.
White-label fits operators who need to launch a branded driver experience in 60 days and accept that the vendor’s platform shapes the customer experience for years afterward; the white-label evaluation guide walks through those trade-offs. Custom development fits operators whose brand and unit economics depend on owning the driver experience, the settlement margin, and the integration topology. The accelerator middle path fits teams that want custom architecture and accelerated time-to-market without inheriting a vendor’s roadmap; accelerators contribute the proven modules (OCPI integration, identity scaffolding, async event handling) and leave the brand-differentiating surfaces (driver UX, tariff logic, partner integrations) for the operator to own.